ITS International Business Assistance Center
Marketing
- Home
- Marketing
- Company Introduction
Company Introduction
Introduce Korean ITS companies
Penta Security Systems Inc.
- Web Site : http://www.pentasecurity.com
- Name : Jeiff Kim
- Department : AutoCrypt Business Div.
- Tel : 82-2-2125-6739
- Fax : -
- E-mail : Jeiff.kim@pentasecurity.com
Business Area :
1st Category
※ Others-
2nd Category
Software,ConsultingOn going project or R&D :
Designed the security and authentication system for C-ITSSecurity solution for C-ITS Implementation Project – Korean Highway/Seoul city/Jeju IslandITS Product & Technologies :
Technologies
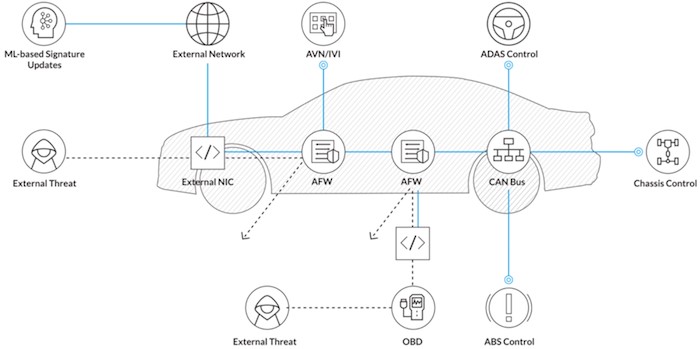
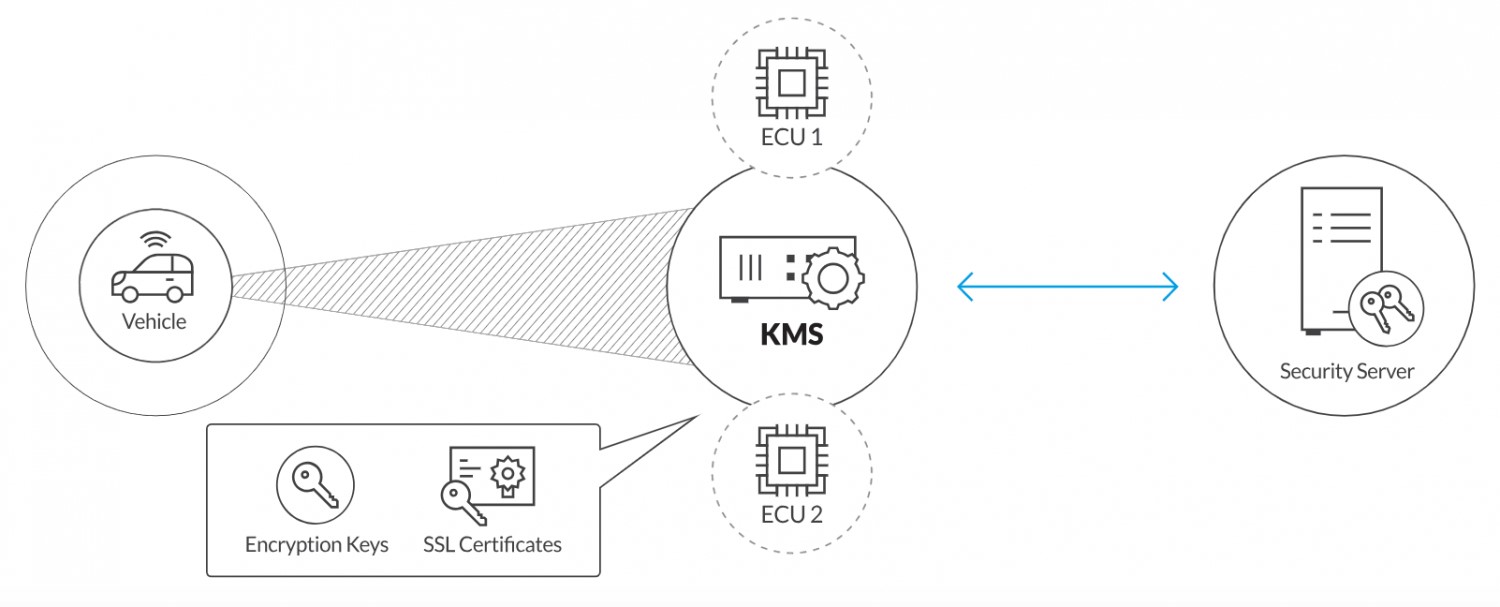
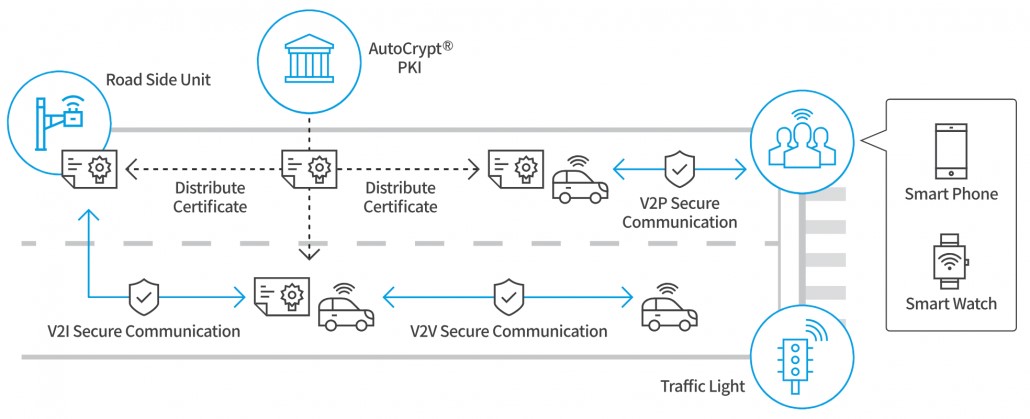
For Intelligent Transport Systems (C-ITS)80% of cars will be connected by 2020. To help create a more convenient tomorrow, connected cars and IoT devices on the road will be engaging in constant communication with a wide range of entities, including unknown ones. This raises the issue of how to prevent untrustworthy communication from entering the traffic infrastructure.Secure communication can be achieved with mutual authentication, which prevents the introduction of fraudulent or malicious traffic information that could endanger lives on the road. In the case of intelligent transport systems (ITS), trusted communication can be established via the implementation of a security credential management system (SCMS).AutoCrypt V2X and AutoCrypt PKI provide the core security components required to protect communications in ITS. For Connected car (In-Vehicle Security)Unlike smart phones, connected vehicles are smart devices that people travel in, rather than with. This means cyber mishaps can instantly become life-threatening. Upon gaining access to a vehicle’s internal network, malicious actors may install new firmware for executing custom commands and take over controls remotely.From the OBD-II port to the vehicle’s wireless connection, the attack vectors for hackers are plenty and aren’t easy to secure. Cars are not just becoming connected, but also autonomous and therefore architecturally extremely complex. All this data being exchanged within the vehicle needs to be monitored for signs of abnormal activity that could indicate network intrusions or attacks.AutoCrypt AFW and AutoCrypt KMS protect the internal systems of vehicles by detecting malicious or abnormal traffic and securely managing encryption keys used within internal networks.TechnologiesAutoCrypt PKIAutoCrypt PKI is a public key infrastructure (PKI) system that complements AutoCrypt V2X by providing certificate management used to authenticate end entities such as cars and traffic lights in an ITS.• Enrolls new end entities into the system, provisions identification and pseudonym certificates, and revokes certificates based on reported misbehavior.• Designed to comply with the CAMP Security Credential Management System (SCMS), with solutions also available for the European Cooperative (C-ITS) Credential Management System (CCMS).AutoCrypt V2XAutoCrypt V2X is an authentication/encryption system for vehicle-to-everything (V2X) communications, including vehicle-to-vehicle (V2V), vehicle-to-infrastructure (V2I), vehicle-to-pedestrian (V2P).• Secures broadcast and receipt of basic safety messages (BSM) and other data between surrounding vehicle on-board units (OBU) and roadside units (RSU).• Designed according to the IEEE 1609.2 communication standard for Wireless Access in Vehicular Environments (WAVE).• AutoCrypt LCM is a local certificate manager (LCM) that is installed in the OBU to manage certificates from AutoCrypt PKI.IEEE1609.2: Wireless Access in Vehicular Environments--Security Services for Applications and Management MessagesCAMP SCMS: Crash Avoidance Metrics Partnership –Security Credential Management System AutoCrypt AFWAutoCrypt AFW offers both a firewall (F/W) and an intrusion detection system (IDS) for in-vehicle networks. It controls and analyzes the network packets in the CAN or Ethernet to protect the network from malicious packets or other abnormal activities.• Implements both positive and negative security models to manage access to in-vehicle systems.• Uses an internal AFW and an external AFW with different security policies.• Uses machine learning (ML) to analyze malicious traffic and provide signature updates to AutoCrypt AFW. AutoCrypt KMSAutoCrypt KMS is an in-vehicle key management system (KMS) that manages keys used for encrypting data transmitted between the vehicle and external entities, or between electronic control units (ECU), as well as keys used for authenticating users and entities.• Manages the encryption key life cycle process which includes generation, storage, and revocation.• Integrates with external key management systems and hardware security modules (HSM).- Previous PARKING CLOUD CO. LTD
- Next LG CNS


